In today’s digital environment, cybersecurity is a critical priority for organizations adopting the Scaled Agile Framework to deliver complex systems and software at scale. As cyber threats continue to grow in sophistication, enterprises must ensure that Agile speed does not come at the cost of data integrity, privacy, or security.
For SAFe® organizations, secure development is not a standalone activity, it must be embedded across teams, value streams, and portfolios. This article explores the key cybersecurity considerations SAFe® teams must implement to enable secure, resilient, and compliant Agile delivery.
### 1. Integrating Cybersecurity into the SAFe® Framework
Cybersecurity must be built into SAFe® from the start, not treated as a late-stage technical task. SAFe®’s Built-In Quality principle explicitly includes security as a core quality dimension.
By treating cybersecurity as a non-functional requirement (NFR), SAFe® teams ensure that security is addressed throughout the development lifecycle. This approach embeds security expectations into every Agile Release Train® (ART®), reducing vulnerabilities and minimizing rework later in the lifecycle.
Security becomes a shared responsibility across planning, execution, and delivery, not an afterthought.
### 2. Adopting a Shift-Left Approach to Security
A shift-left security strategy enables SAFe® teams to identify and remediate vulnerabilities early, when fixes are faster and less costly.
Rather than waiting until the end of development, security checks are integrated into the CI/CD pipeline, allowing teams to:
* Detect vulnerabilities early
* Automate security testing
* Maintain rapid release cycles
This approach supports both speed and safety, enabling teams to release frequently without compromising their security posture.
### 3. Security by Design
Security is most effective when addressed during the design and architecture phases.
SAFe® teams should incorporate:
* Secure coding standards
* Threat modeling
* Architecture and design reviews
By embedding security into system design, organizations prevent vulnerabilities rather than patching them later. Close collaboration between development, security, and operations teams ensures security controls are seamlessly integrated into workflows.
This collaboration aligns naturally with DevSecOps, where security is embedded across the delivery pipeline.
### 4. Ensuring Continuous Compliance
For organizations operating in regulated industries, compliance is non-negotiable. SAFe® enables continuous compliance through regular reviews and feedback loops.
Security and compliance checks can be integrated into:
* Program Increment (PI) Planning
* Inspect & Adapt (I&A) workshops
This allows teams to proactively identify compliance risks and address them early. By adopting DevSecOps practices, SAFe® teams can maintain compliance while continuing to deliver value at speed.
This approach supports adherence to regulations such as General Data Protection Regulation (GDPR), The Health Insurance Portability and Accountability Act (HIPAA), and other industry-specific standards.
### 5. Enhancing Security within the Agile Release Train (ART)
Security must be visible and enforced at the ART® level. The Release Train Engineer® (RTE®) plays a key role in ensuring that cybersecurity considerations are included in planning, execution, and delivery.
Many organizations also designate security champions within Agile® teams. These individuals:
* Advocate security best practices
* Act as local security points of contact
* Help teams stay aligned with security standards
This distributed ownership model ensures security is embedded across the ART® rather than centralized in a single function.
### 6. Protecting Data and Privacy
Data protection is a core cybersecurity concern. SAFe® teams must implement strong safeguards such as:
* Encryption
* Data masking
* Anonymization
These practices protect sensitive data across development and production environments.
Privacy protection must also be built into development processes to ensure compliance with global regulations such as California Consumer Privacy Act (CCPA). Embedding privacy-by-design principles helps organizations maintain customer trust and reduce regulatory risk.
### 7. Preparing for Incident Response and Recovery
Even the most secure systems can experience incidents. SAFe® teams must be prepared with:
* A clearly defined incident response plan
* Escalation paths across teams and leadership
* Regular response simulations and training
Disaster recovery planning should also be integrated into Agile® practices. A well-prepared recovery strategy minimizes downtime, reduces business impact, and enables rapid restoration of services.
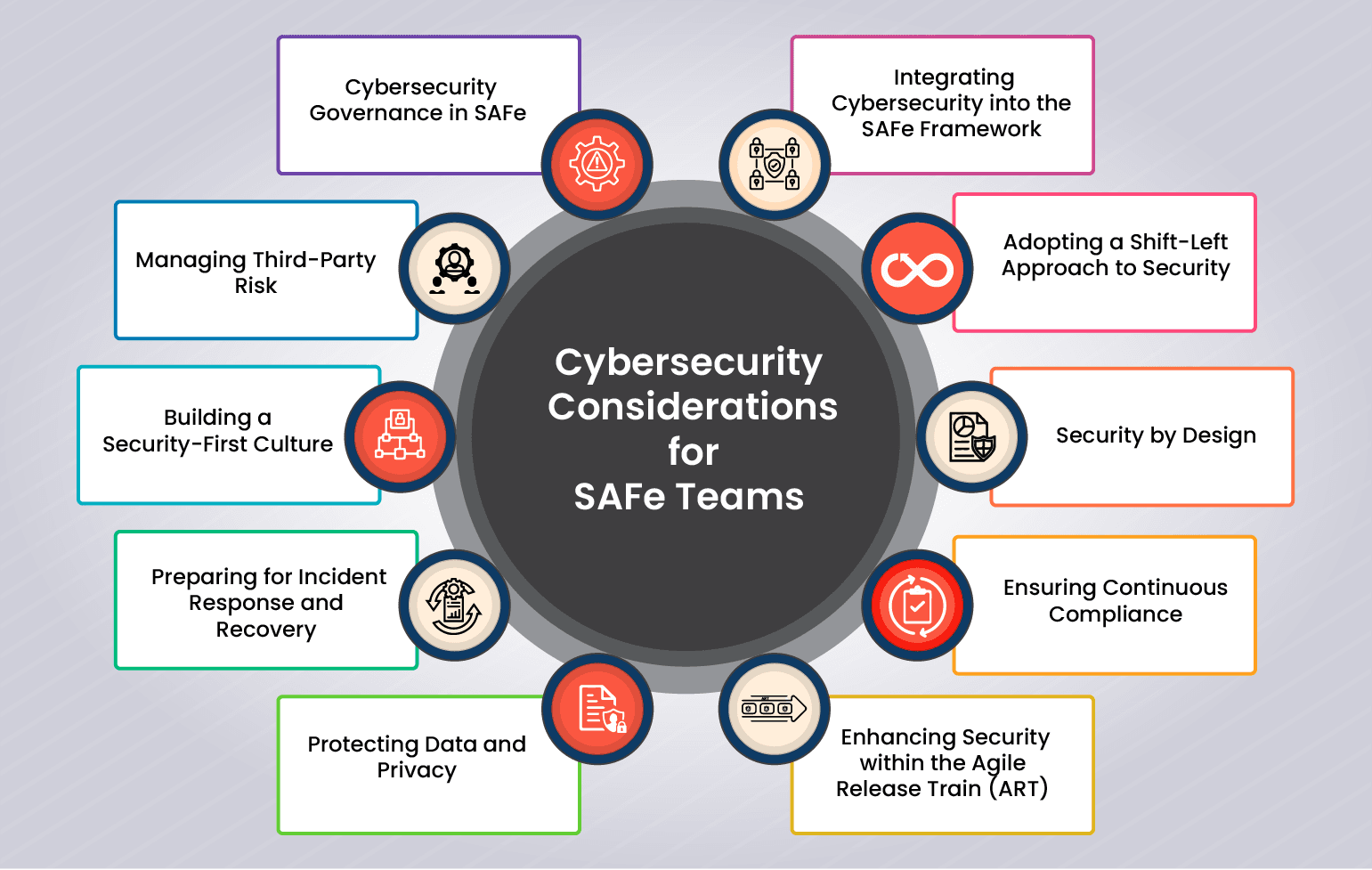
### 8. Building a Security-First Culture
Cybersecurity is not just a technical practice, it is a cultural mindset.
SAFe® organizations should foster a security-first culture by:
* Providing regular security awareness training
* Encouraging secure development behaviors
* Conducting blameless post-mortems after incidents
This approach promotes learning and continuous improvement rather than fear or blame, strengthening long-term security maturity.
### 9. Managing Third-Party Risk
Third-party vendors and tools can introduce security risks. It’s essential to establish strict vendor security requirements and vet all third-party providers to ensure they meet the organization’s standards. Supply chain security should be a top consideration, as vulnerabilities in third-party software are a common attack vector.
For example, a financial institution enforced strict security protocols for third-party vendors, avoiding potential vulnerabilities and safeguarding their platform from supply chain attacks.
### 10. Cybersecurity Governance in SAFe
Effective cybersecurity governance must align with enterprise strategy. By integrating security considerations into Lean Portfolio Management (LPM), organizations balance agility with necessary controls.
This ensures:
* Security priorities align with business objectives
* Portfolio investments support risk reduction
* ARTs® operate within clear security guardrails
Cybersecurity governance at the portfolio level enables consistent security practices without slowing Agile® delivery.
### Conclusion: Achieving Agility Without Compromising Security
As organizations scale Agile® delivery through SAFe®, cybersecurity must remain foundational. By embedding security into design, development, governance, and culture, SAFe® teams can deliver value rapidly without compromising trust or resilience.
Practices such as shift-left security, continuous compliance, DevSecOps, and portfolio-level governance allow organizations to maintain speed while protecting critical assets.
With the right cybersecurity approach, SAFe® teams can confidently scale Agile®, delivering innovation, security, and reliability together.
**Related Courses & Certification Training:** [SAFe® for Teams (SP)](https://skillbookacademy.com/courses/safe-for-teams-sp-certification-training) | [SAFe® Release Train Engineer (RTE)](https://skillbookacademy.com/courses/safe-release-train-engineer-rte-certification-training) | [SAFe® Practice Consultant Certification Training](https://skillbookacademy.com/courses/safe-practice-consultant-certification-training) | [Certified Scrum Master (CSM)](https://skillbookacademy.com/courses/certified-scrum-master-csm-certification-training) | [SAFe® Agile Product Management Certification Training](https://skillbookacademy.com/courses/safe-agile-product-management-certification-training)